Where Are Certificates Stored Windows 10
First published on TechNet on Mar 05, 2018
Hello all! Nathan Penn and Jason McClure hither to embrace some PKI basics, techniques to effectively manage certificate stores, and also provide a script nosotros developed to bargain with common certificate store issue we have encountered in several enterprise environments (certificate truncation due to besides many installed certificate regime).
To get started we need to review some core concepts of how PKI works. Equally you scan secure sites on the Internet and/or within your organisation, your computer leverages certificates to build trust with the remote site it is communicating with. Some of these certificates are local and installed on your estimator, while some are installed on the remote site. If we were to browse to https://support.microsoft.com we would notice:


The lock lets us know that the communication between our calculator and the remote site is encrypted. But why, and how do nosotros establish that trust? When we typed https://back up.microsoft.com,the site on the other finish sent its document that looks like this:
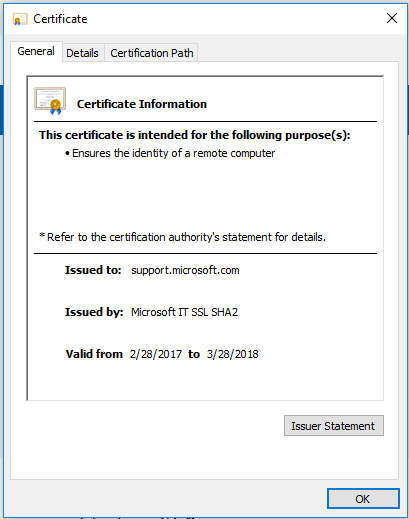
We won't go into the process the owner of the site went through to get the certificate, as the process varies for certificates used inside an system versus certificates used for sites exposed to the Net. Regardless of the process used by the site to go the certificate, the Certificate Concatenation, also called the Certification Path, is what establishes the trust relationship between the computer and the remote site and is shown below.

As you can run into, the document concatenation is a hierarchal collection of certificates that leads from the certificate the site is using (support.microsoft.com), back to a root of trust, the Trusted Root Certification Authority (CA). In the above example, DigiCert Baltimore Root is the Trusted Root CA. All certificates in between the site'due south document and the Trusted Root CA certificate, are Intermediate Document Potency certificates. To establish the trust human relationship between a computer and the remote site, the computer must take the entirety of the certificate concatenation installed within what is referred to as the local Certificate Store. When this happens, a trust can be established and you lot get the lock icon shown above. But, if nosotros are missing certs or they are in the incorrect location we get-go to see this error:

The document store is separated into two primary components, a Computer store & a User store. The primary divergence being that certificates loaded into the Calculator shop go global to all users on the reckoner, while certificates loaded into the User store are only attainable to the logged on user. To keep things uncomplicated, we will focus solely on the Computer store in this post. Leveraging the Certificates MMC (certmgr.msc), we accept a convenient interface to quickly and visually identify the certificates currently loaded into the local Certificate Shop. This tool also provides us the adequacy to efficiently review what certificates have been loaded, and if the certificates accept been loaded into the correct location. This means nosotros accept the ability to view the certificates that have been loaded as Trusted Root CAs, Intermediate CAs, and/or both (hmmm… that doesn't audio correct).

Identifying a Root CA from an Intermediate CA is a fairly uncomplicated concept to understand once explained. Trusted Root CAs are the certificate authority that establishes the acme level of the hierarchy of trust. Past definition this means that whatever certificate that belongs to a Trusted Root CA is generated, or issued, by itself. Understanding this makes identifying a Trusted Root CA certificate exceptionally easy to identify equally the "Issued To" and "Issued By" attributes will always friction match.

Alternatively, an Intermediate CA is a Certificate Authorization that builds upon the trust of some other CA. This can be either, another Intermediate CA, or a Trusted Root CA. Agreement this makes identifying an Intermediate CA document just equally like shooting fish in a barrel as the "Issued To" and "Issued By" attributes must exist dissimilar.

To sum upwards a Trusted Root CA is issued by itself, while an Intermediate CA is issued by something else. Uncomplicated stuff, right?
We know most remote site certificates, the certificate chain they rely on, the local certificate store, and the difference between Root CAs and Intermediate CAs at present. But what nearly managing it all? On individual systems that are not domain joined, managing certificates can exist easily accomplished through the same local Certificates MMC shown previously. In addition to existence able to view the certificates currently loaded, the console provides the capability to import new, and delete existing certificates that are located within.


On a domain joined systems it is recommended to manage PKI at the enterprise level (which may explicate why we named 1 of the MMC Enterprise PKI). This is done through the Group Policy MMC (gpmc.msc), and nosotros would typically make the changes to a single policy linked at the domain level. Using this approach, we can ensure that all systems in the domain have the same certificates loaded and in the appropriate store. It too provides the ability to add new certificates and remove unnecessary certificates as needed.

On several occasions both of us take gone into enterprise environments experiencing hallmark oddities, and after a little analysis trace the event to an Schannel event 36885.

This event is caused by the number of certificates loaded into the estimator'south Trusted Root Certificate Authorities (TRCA) and Intermediate Certificate Regime (ICA) stores. The most of import role of the higher up alarm is the following: "Currently, this server trusts so many certificate authorities that the list has grown too long. This list has thus been truncated." Unfortunately, here is what nosotros don't know: Where was the list truncated, which certificate authorities did information technology take hold of, which certificate authorities did information technology Non grab, and do I have all the certs that will be needed to build whatever of the given document chains for the requests that will be made? At this point many of you are request, "How many is too many?" The answer to this is information technology depends, as the limitation is based on the size of the shop which is limited to sixteen kilobytes and not the number of certificates. In December 2012, KB931125 was released and intended simply for client SKUs. However, information technology was as well offered for Server SKUs for a short fourth dimension on Windows Update and WSUS. This package installed all TRCAs enrolled in the Microsoft Trusted Root Program (more than 330). While we offer a fix it tool for individual systems here (SSL/TLS communication problems afterward you install KB 931125 - Windows Server), this wasn't identified as an issue in several environments. On a small scale, customers that feel certificate bloat bug can leverage the Certificate MMC to deal with the effect on individual systems. Unfortunately, the ability to articulate the certificate store on clients and servers on a targeted and massive calibration with minimal effort does not exist. On a larger calibration, customers would be required to leverage the Microsoft built-in "Certutil" awarding via a script. This technique requires the scripter to identify and code in the thumbprint of every certificate that is to be purged on each system (likewise very labor intensive).
CertPurge volition remove all locally installed certificates from the Trusted Root Certification Authorities, Intermediate Certification Authorities, and 3rd-Political party Root Certification Authorities stores on the local motorcar. Merely certificates that are being deployed to the machine from Group Policy will remain.
The power to articulate the certificate store on clients and servers on a targeted and massive scale with minimal effort. This is needed to handle document bloat problems that can ultimately effect in authentication issues. On a small-scale scale, customers that experience document bloat bug can leverage the built-in document MMC to deal with the issue on a system by system ground every bit a manual process. On a larger scale, customers would exist required to leverage the Microsoft congenital-in "Certutil" application via a script. This technique requires the scripter to identify and code in the thumbprint of every certificate that is to be purged on each system (besides very labor intensive).
CertPurge scans the post-obit registry locations ("HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates" & "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates") and builds an array for all entries found under the Trusted Root Certification Authorities, Intermediate Certification Regime, and Third-Political party Root Certification Authorities paths. CertPurge then leverages the array to delete every subkey.
Prior to performing whatsoever operations (i.e. building array, purging certificates), CertPurge generates a backup of the "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates" & "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates" paths in their entirety into a .reg file stored in the c:\windows\ directory. In the event that required certificates are purged, an administrator tin import the fill-in files and restore all purged certificates. (NOTE: This is a manual process, and then testing prior to implementation on a mass scale is highly recommended).
Certificates pushed via GPO are stored in the "HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\SystemCertificates" path. As CertPurge does non target this location, all certificates deployed via GPO are unaffected.
KB 293781 details the certificates that are required for the operating organisation to operate correctly. Removal of the certificates identified in the article may limit functionality of the operating system or may crusade the computer to fail. Ensure at a minimum that these certificates are published via a GPO prior to implementing the CertPurge awarding\script. If a required document (either one from the KB, or one specific to the customer environs) is purged, that is not being deployed via GPO, the recommended approach is as follows
one. Restore certificates to an individual machine using the backup registry file,
2. Leveraging the Certificate MMC, export the required certificates to file,
3. Update the GPO that is deploying certificates by importing the required certificates,
4. Rerun CertPurge on machine identified in footstep one to re-purge all certificates,
5. Execute a GPUpdate on machine identified in step 1 to receive updated GPO certificate deployment,
half-dozen. TEST!!!
vii. Did nosotros mention Test?
At this point, hopefully we all empathise some of the basics, what a document chain is, the difference in a Root document and an Intermediate/Issuing certificate, and where those certificates should exist located on our systems. Likewise, we now take a method for cleaning things up things in bulk should things get out of control and you need to re-baseline systems in mass. Allow us know what you all think, and if in that location is some other area you want the states to aggrandize on next.
Additional Resources:
Failed TLS connection between unified communications peers generates an Schannel warning (microsoft....SSL/TLS communication problems after you install KB 931125 - Windows Server
Configure Trusted Roots and Disallowed Certificates
Disclaimer The sample scripts are not supported nether any Microsoft standard back up program or service. The sample scripts are provided Equally IS without warranty of whatsoever kind. Microsoft further disclaims all implied warranties including, without limitation, any implied warranties of merchantability or of fitness for a particular purpose. The unabridged risk arising out of the use or operation of the sample scripts and documentation remains with you. In no event shall Microsoft, its authors, or anyone else involved in the creation, product, or delivery of the scripts be liable for any damages whatsoever (including, without limitation, damages for loss of business profits, business concern interruption, loss of business data, or other pecuniary loss) arising out of the employ of or disability to use the sample scripts or documentation, even if Microsoft has been advised of the possibility of such damages.
Download CertPurge.ps1 here
Where Are Certificates Stored Windows 10,
Source: https://techcommunity.microsoft.com/t5/core-infrastructure-and-security/pki-basics-how-to-manage-the-certificate-store/ba-p/259419
Posted by: olivasbobsoo.blogspot.com


0 Response to "Where Are Certificates Stored Windows 10"
Post a Comment